
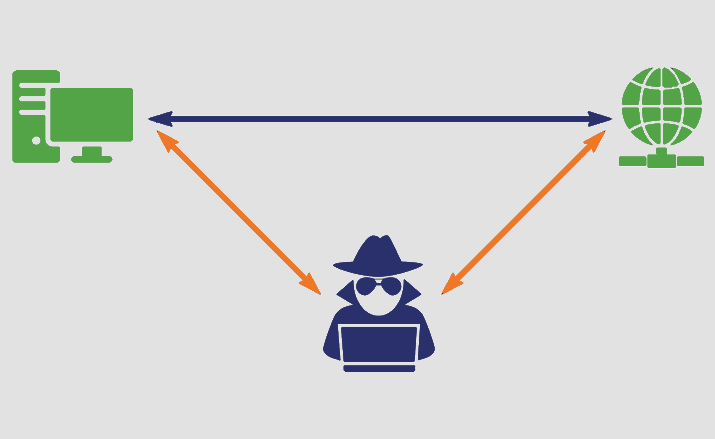
The man in attack is a general term which is used for the person who is a culprit positions himself in a conversation between a client and an application either to listen in or to imitate one of the gatherings, causing it to show up as though an ordinary trade of data is in progress.
The objective of an attack is to take individual data, for example, login credentials, account subtleties and financial card numbers. Targets are regularly the clients of money related applications, SaaS organizations, internet business locales and different sites where signing in is required.
Data acquired during an assault could be utilized for some reasons, including fraud, unapproved reserve moves or password change.
For suppose you received an email that displays you that it is from your bank, instruct you to log in to your account to confirm your details and data. Eventually, if you click on the link mentioned in the email and it will look exactly like your bank website, where you have log in and entered your details. In that case, the man in the center (MITM)
In such a situation, the man in the center (MITM) sent you the email, causing it to seem, by all accounts, to be genuine. (This assault additionally includes phishing, getting you to tap on the email seeming to originate from your bank.) The culprit likewise made a site that looks simply like your bank's site, so you wouldn't delay to enter your login qualifications in the wake of tapping the connection in the email. However, when you do that, you're not signing into your ledger, you're giving over your qualifications to the aggressor.
Man in browse attack: With a man-in-the-program assault (MITB), an assailant needs an approach to infuse noxious programming, or malware, into the unfortunate casualty's PC or Smartphone. One of the manners in which this can be accomplished is by phishing.
Phishing is the point at which a fraudster sends an email or instant message to a client that seems to start from confided in source, for example, a bank, as in our unique model. By clicking on a connection or opening a connection in the phishing message, the client can accidentally stack malware onto their device.
The malware then introduces itself on the program without the client's information. The malware records the information sent between the person in question and explicit focused on sites, for example, budgetary foundations, and transmit it to the assailant.
Blocking MITM assaults requires a few easy ventures with respect to clients, just as a blend of encryption and check techniques for applications.
For clients, this implies:
For site administrators, secure correspondence conventions, including TLS and HTTPS; help relieve mocking attacks by heartily encoding and validating transmitted information. Doing as such avoids the capture of site traffic and hinders the unscrambling of delicate information, for example, validation tokens.
It is viewed as a best practice for applications to utilize SSL/TLS to verify each page of their site and not simply the pages that expect clients to sign in. Doing as such helps diminishes the opportunity of an aggressor taking session treats from a client perusing on an unbound segment of a site while signed in.